
Biometrics
Encyclopedia

Biostatistics
Biostatistics is the application of statistics to a wide range of topics in biology...
[36]" (wikilink added to original quote).
consists of methods for uniquely recognizing humans based upon one or more intrinsic physical or behavioral traits. In computer science
Computer science
Computer science or computing science is the study of the theoretical foundations of information and computation and of practical techniques for their implementation and application in computer systems...
, in particular, biometrics is used as a form of identity access management and access control
Access control
Access control refers to exerting control over who can interact with a resource. Often but not always, this involves an authority, who does the controlling. The resource can be a given building, group of buildings, or computer-based information system...
. It is also used to identify individuals in groups that are under surveillance
Surveillance
Surveillance is the monitoring of the behavior, activities, or other changing information, usually of people. It is sometimes done in a surreptitious manner...
.
Biometric identifiers are the distinctive, measurable characteristics used to identify individuals. The two categories of biometric identifiers include physiological and behavioral characteristics. Physiological characteristics are related to the shape of the body, and include but are not limited to: fingerprint
Fingerprint
A fingerprint in its narrow sense is an impression left by the friction ridges of a human finger. In a wider use of the term, fingerprints are the traces of an impression from the friction ridges of any part of a human hand. A print from the foot can also leave an impression of friction ridges...
, face recognition
Facial recognition system
A facial recognition system is a computer application for automatically identifying or verifying a person from a digital image or a video frame from a video source...
, DNA
DNA
Deoxyribonucleic acid is a nucleic acid that contains the genetic instructions used in the development and functioning of all known living organisms . The DNA segments that carry this genetic information are called genes, but other DNA sequences have structural purposes, or are involved in...
, palm print
Palm print
A palm print refers to an image acquired of the palm region of the hand. It can be either an online image or offline image where the image is taken with ink and paper ....
, hand geometry, iris recognition
Iris recognition
Iris recognition is an automated method of biometric identification that uses mathematical pattern-recognition techniques on video images of the irides of an individual's eyes, whose complex random patterns are unique and can be seen from some distance....
(which has largely replaced retina
Retinal scan
A retinal scan is a biometric technique that uses the unique patterns on a person's retina to identify them. It is not to be confused with another ocular-based technology, iris recognition.-Introduction:...
), and odour/scent. Behavioral characteristics are related to the behavior of a person, including but not limited to: typing rhythm
Keystroke dynamics
Keystroke dynamics, or typing dynamics, is the detailed timing information that describes exactly when each key was pressed and when it was released as a person is typing at a computer keyboard.- Science of Keystroke Dynamics :...
, gait
Gait analysis
Gait analysis is the systematic study of animal locomotion, more specific as a study of human motion, using the eye and the brain of observers, augmented by instrumentation for measuring body movements, body mechanics, and the activity of the muscles. Gait analysis is used to assess, plan, and...
, and voice
Speaker recognition
Speaker recognition is the computing task of validating a user's claimed identity using characteristics extracted from their voices .There is a difference between speaker recognition and speech recognition . These two terms are frequently confused, as is voice recognition...
Strictly speaking, voice is also a physiological trait because every person has a different vocal tract
Vocal tract
The vocal tract is the cavity in human beings and in animals where sound that is produced at the sound source is filtered....
, but voice recognition is mainly based on the study of the way a person speaks, commonly classified as behavioral. Biometric voice recognition is separate and distinct from speech recognition
Speech recognition
Speech recognition converts spoken words to text. The term "voice recognition" is sometimes used to refer to recognition systems that must be trained to a particular speaker—as is the case for most desktop recognition software...
with the latter being concerned with accurate understanding of speech content rather than identification or recognition of the person speaking.. Some researchers have coined the term behaviometrics to describe the latter class of biometrics.
More traditional means of access control include token-based identification systems, such as a driver's license
Driver's license
A driver's license/licence , or driving licence is an official document which states that a person may operate a motorized vehicle, such as a motorcycle, car, truck or a bus, on a public roadway. Most U.S...
or passport
Passport
A passport is a document, issued by a national government, which certifies, for the purpose of international travel, the identity and nationality of its holder. The elements of identity are name, date of birth, sex, and place of birth....
, and knowledge-based identification systems, such as a password
Password
A password is a secret word or string of characters that is used for authentication, to prove identity or gain access to a resource . The password should be kept secret from those not allowed access....
or personal identification number
Personal identification number
A personal identification number is a secret numeric password shared between a user and a system that can be used to authenticate the user to the system. Typically, the user is required to provide a non-confidential user identifier or token and a confidential PIN to gain access to the system...
. Since biometric identifiers are unique to individuals, they are more reliable in verifying identity than token and knowledge-based methods, however, the collection of biometric identifiers raises privacy concerns about the ultimate use of this information.
Biometric functionality
Many different aspects of human physiology, chemistry or behavior can be used for biometric authentication. The selection of a particular biometric for use in a specific application involves a weighting of several factors. Jain et al. (1999) identified seven such factors to be used when assessing the suitability of any trait for use in biometric authentication. Universality means that every person using a system should possess the trait. Uniqueness means the trait should be sufficiently different for individuals in the relevant population such that they can be distinguished from one another. Permanence relates to the manner in which a trait varies over time. More specifically, a trait with 'good' permanence will be reasonably invariant over time with respect to the specific matching algorithm. Measurability (collectability) relates to the ease of acquisition or measurement of the trait. In addition, acquired data should be in a form that permits subsequent processing and extraction of the relevant feature sets. Performance relates to the accuracy, speed, and robustness of technology used (see performance section for more details). Acceptability relates to how well individuals in the relevant population accept the technology such that they are willing to have their biometric trait captured and assessed. Circumvention relates to the ease with which a trait might be imitated using an artifact or substitute.No single biometric will meet all the requirements of every possible application.
Authentication
Authentication is the act of confirming the truth of an attribute of a datum or entity...
mode the system performs a one-to-one comparison of a captured biometric with a specific template stored in a biometric database in order to verify the individual is the person they claim to be. This process may use a smart card
Smart card
A smart card, chip card, or integrated circuit card , is any pocket-sized card with embedded integrated circuits. A smart card or microprocessor cards contain volatile memory and microprocessor components. The card is made of plastic, generally polyvinyl chloride, but sometimes acrylonitrile...
, username or ID number (e.g. PIN
Personal identification number
A personal identification number is a secret numeric password shared between a user and a system that can be used to authenticate the user to the system. Typically, the user is required to provide a non-confidential user identifier or token and a confidential PIN to gain access to the system...
) to indicate which template should be used for comparison.Systems can be designed to use a template stored on media like an e-Passport
Biometric passport
A biometric passport, also known as an e-passport or ePassport, is a combined paper and electronic passport that contains biometric information that can be used to authenticate the identity of travelers...
or smart card
Smart card
A smart card, chip card, or integrated circuit card , is any pocket-sized card with embedded integrated circuits. A smart card or microprocessor cards contain volatile memory and microprocessor components. The card is made of plastic, generally polyvinyl chloride, but sometimes acrylonitrile...
, rather than a remote database. 'Positive recognition' is a common use of verification mode, "where the aim is to prevent multiple people from using same identity".
In Identification mode the system performs a one-to-many comparison against a biometric database in attempt to establish the identity of an unknown individual. The system will succeed in identifying the individual if the comparison of the biometric sample to a template in the database falls within a previously set threshold. Identification mode can be used either for 'positive recognition' (so that the user does not have to provide any information about the template to be used) or for 'negative recognition' of the person "where the system establishes whether the person is who she (implicitly or explicitly) denies to be". The latter function can only be achieved through biometrics since other methods of personal recognition such as passwords, PINs or keys are ineffective.
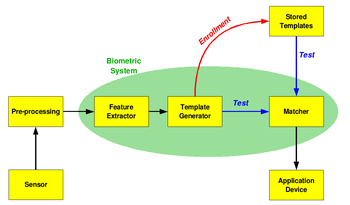
The first time an individual uses a biometric system is called enrollment. During the enrollment, biometric information from an individual is captured and stored. In subsequent uses, biometric information is detected and compared with the information stored at the time of enrollment. Note that it is crucial that storage and retrieval of such systems themselves be secure if the biometric system is to be robust. The first block (sensor) is the interface between the real world and the system; it has to acquire all the necessary data. Most of the times it is an image acquisition system, but it can change according to the characteristics desired. The second block performs all the necessary pre-processing: it has to remove artifacts from the sensor, to enhance the input (e.g. removing background noise), to use some kind of normalization, etc. In the third block necessary features are extracted. This step is an important step as the correct features need to be extracted in the optimal way. A vector of numbers or an image with particular properties is used to create a template. A template is a synthesis of the relevant characteristics extracted from the source. Elements of the biometric measurement that are not used in the comparison algorithm are discarded in the template to reduce the filesize and to protect the identity of the enrollee.
If enrollment is being performed, the template is simply stored somewhere (on a card or within a database or both). If a matching phase is being performed, the obtained template is passed to a matcher that compares it with other existing templates, estimating the distance between them using any algorithm (e.g. Hamming distance
Hamming distance
In information theory, the Hamming distance between two strings of equal length is the number of positions at which the corresponding symbols are different...
). The matching program will analyze the template with the input. This will then be output for any specified use or purpose (e.g. entrance in a restricted area).
Performance
The following are used as performance metrics for biometric systems:- false accept rate or false match rate (FAR or FMR): the probability that the system incorrectly matches the input pattern to a non-matching template in the database. It measures the percent of invalid inputs which are incorrectly accepted.
- false reject rate or false non-match rate (FRR or FNMR): the probability that the system fails to detect a match between the input pattern and a matching template in the database. It measures the percent of valid inputs which are incorrectly rejected.
- receiver operating characteristicReceiver operating characteristicIn signal detection theory, a receiver operating characteristic , or simply ROC curve, is a graphical plot of the sensitivity, or true positive rate, vs. false positive rate , for a binary classifier system as its discrimination threshold is varied...
or relative operating characteristic (ROC): The ROC plot is a visual characterization of the trade-off between the FAR and the FRR. In general, the matching algorithm performs a decision based on a threshold which determines how close to a template the input needs to be for it to be considered a match. If the threshold is reduced, there will be less false non-matches but more false accepts. Correspondingly, a higher threshold will reduce the FAR but increase the FRR. A common variation is the Detection error trade-off (DET), which is obtained using normal deviate scales on both axes. This more linear graph illuminates the differences for higher performances (rarer errors). - equal error rate or crossover error rate (EER or CER): the rate at which both accept and reject errors are equal. The value of the EER can be easily obtained from the ROC curve. The EER is a quick way to compare the accuracy of devices with different ROC curves. In general, the device with the lowest EER is most accurate.
- failure to enroll rate (FTE or FER): the rate at which attempts to create a template from an input is unsuccessful. This is most commonly caused by low quality inputs.
- failure to capture rate (FTC): Within automatic systems, the probability that the system fails to detect a biometric input when presented correctly.
- template capacity: the maximum number of sets of data which can be stored in the system.
History of Biometrics
People may think that biometrics is a recent advancement, but biometrics has been around since 29,000 BC when cavemen would sign their drawings with handprints. In 500 BC Babylonian business transactions were signed in clay tablets with fingerprints. The earliest cataloging of fingerprints dates back to 1881 when Juan Vucetich started a collection of fingerprints of criminals in Argentina.The History of Fingerprints.
Proposal calls for biometric authentication to access certain public networks
John Michael (Mike) McConnell, a former vice admiral in the United States NavyUnited States Navy
The United States Navy is the naval warfare service branch of the United States Armed Forces and one of the seven uniformed services of the United States. The U.S. Navy is the largest in the world; its battle fleet tonnage is greater than that of the next 13 largest navies combined. The U.S...
, a former Director of US National Intelligence
United States Director of National Intelligence
The Director of National Intelligence , is the United States government official subject to the authority, direction and control of the President, who is responsible under the Intelligence Reform and Terrorism Prevention Act of 2004 for:...
, and Senior Vice President of Booz Allen Hamilton
Booz Allen Hamilton
Booz Allen Hamilton Inc. , or more commonly Booz Allen, is an American public consulting firm headquartered in McLean, Fairfax County, Virginia, with 80 other offices throughout the United States. Ralph Shrader is its Chairman and Chief Executive Officer. The firm was founded by Edwin Booz in...
promoted the development of a future capability to require biometric authentication to access certain public networks in his Keynote Speech at the 2009 Biometric Consortium Conference.
A basic premise in the above proposal is that the person that has uniquely authenticated themselves using biometrics with the computer is in fact also the agent performing potentially malicious actions from that computer. However, if control of the computer has been subverted, for example in which the computer is part of a botnet
Botnet
A botnet is a collection of compromised computers connected to the Internet. Termed "bots," they are generally used for malicious purposes. When a computer becomes compromised, it becomes a part of a botnet...
controlled by a hacker, then knowledge of the identity of the user at the terminal does not materially improve network security or aid law enforcement activities .
Recently, another approach to biometric security was developed, this method scans the entire body of prospects to guarantee a better identification of this prospect. This method is not globally accepted because it is very complex and prospects are concerned about their privacy. Very few technologists apply it globally.
Privacy and discrimination
It is possible that data obtained during biometric enrollment may be used in ways for which the enrolled individual has not consented. For example, biometric security that utilizes an employee's DNA profile could also be used to screen for various genetic diseases or other 'undesirable' traits.Danger to owners of secured items
When thieves cannot get access to secure properties, there is a chance that the thieves will stalk and assault the property owner to gain access. If the item is secured with a biometric device, the damage to the owner could be irreversible, and potentially cost more than the secured property. For example, in 2005, Malaysian car thieves cut off the finger of a Mercedes-Benz S-ClassMercedes-Benz S-Class
The Mercedes-Benz S-Class is a series of luxury sedans produced by Mercedes-Benz, a division of Daimler AG. The classification was officially introduced in 1972 with the W116 S-Class, which succeeded previous Mercedes-Benz models dating to the mid-1950s...
owner when attempting to steal the car.
Cancelable biometrics
One advantage of passwords over biometrics is that they can be re-issued. If a token or a password is lost or stolen, it can be cancelled and replaced by a newer version. This is not naturally available in biometrics. If someone's face is compromised from a database, they cannot cancel or reissue it. Cancelable biometrics is a way in which to incorporate protection and the replacement features into biometrics. It was first proposed by Ratha et al.Several methods for generating cancelable biometrics have been proposed. The first fingerprint based cancelable biometric system was designed and developed by Tulyakov et al. Essentially, cancelable biometrics perform a distortion of the biometric image or features before matching. The variability in the distortion parameters provides the cancelable nature of the scheme. Some of the proposed techniques operate using their own recognition engines, such as Teoh et al. and Savvides et al., whereas other methods, such as Dabbah et al., take the advantage of the advancement of the well-established biometric research for their recognition front-end to conduct recognition. Although this increases the restrictions on the protection system, it makes the cancellable templates more accessible for available biometric technologies.
Soft biometrics
Soft biometricsSoft biometrics
Soft Biometrics traits are physical, behavioural or adhered human characteristics, classifiable in pre–defined human compliant categories. These categories are, unlike in the classical biometric case, established and time–proven by humans with the aim of differentiating individuals...
because of their inner nature are privacy preserving. They allow to describe a subject starting from his/her physical attributes. Those attributes have a low discriminating power, thus not capable of identification performance, additionally they are fully available to everyone (e.g. height, weight, gender) which makes them privacy-safe.
International sharing of biometric data
Many countries, including the United States, are planning to share biometric data with other nations.In testimony before the US House Appropriations Committee, Subcommittee on Homeland Security on "biometric identification" in 2009, Kathleen Kraninger and Robert A Mocny commented on international cooperation and collaboration with respect to biometric data, as follows:
According to an article written in 2009 by S. Magnuson in the National Defense Magazine entitled "Defense Department Under Pressure to Share Biometric Data" the United States has bi-lateral agreements with other nations aimed at sharing biometric data. To quote that article:
Governments are unlikely to disclose full capabilities of biometric deployments
Certain members of the civilian community are worried about how biometric data is used. Unfortunately, full disclosure may not be forthcoming to the civilian community.Australia
Visitors intending to visit Australia may soon have to submit to biometric authentication as part of the SmartgateSmartgate
SmartGate is an automated border processing system being introduced by the Australian Customs and Border Protection Service and New Zealand Customs Service. It is a secure and simple system that performs the customs and immigration checks normally made by a Customs Officer when a traveller arrives...
system, linking individuals to their visas and passports. Biometric data are already collected from some visa applicants by Immigration.
Australia is the first country to introduce a Biometrics Privacy Code, which is established and administered by the Biometrics Institute
Biometrics Institute
The Biometrics Institute is the independent Not for profit association providing information, education, research and testing of biometrics. It is predominately a user group representing government departments and private organisations who are using or looking at using biometrics, but suppliers...
. The Biometrics Institute Privacy Code Biometrics Institute forms part of Australian privacy legislation. The Code includes privacy standards that are at least equivalent to the Australian National Privacy Principles (NPPs) in the Privacy Act and also incorporates higher standards of privacy protection in relation to certain acts and practices. Only members of the Biometrics Institute are eligible to subscribe to this Code. Biometrics Institute membership, and thus subscription to this Code, is voluntary.
Brazil
Since the beginning of the 20th century, BrazilBrazil
Brazil , officially the Federative Republic of Brazil , is the largest country in South America. It is the world's fifth largest country, both by geographical area and by population with over 192 million people...
ian citizens have had user ID cards. The decision by the Brazilian government to adopt fingerprint-based biometrics was spearheaded by Dr. Felix Pacheco at Rio de Janeiro
Rio de Janeiro
Rio de Janeiro , commonly referred to simply as Rio, is the capital city of the State of Rio de Janeiro, the second largest city of Brazil, and the third largest metropolitan area and agglomeration in South America, boasting approximately 6.3 million people within the city proper, making it the 6th...
, at that time capital of the Federative Republic. Dr. Pacheco was a friend of Dr. Juan Vucetich
Juan Vucetich
Juan Vucetich was a Croatian-born Argentine anthropologist and police official who pioneered the use of fingerprinting.-Biography:...
, who invented one of the most complete tenprint classification systems in existence. The Vucetich system was adopted not only in Brazil, but also by most of the other South American countries. The oldest and most traditional ID Institute in Brazil (Instituto de Identificação Félix Pacheco) was integrated at DETRAN (Brazilian equivalent to DMV) into the civil and criminal AFIS
Automated Fingerprint Identification System
Automated fingerprint identification is the process of automatically matching one or many unknown fingerprints against a database of known and unknown prints...
system in 1999.
Each state in Brazil is allowed to print its own ID card, but the layout and data are the same for all of them. The ID cards printed in Rio de Janeiro are fully digitized using a 2D bar code with information which can be matched against its owner off-line. The 2D bar code encodes a color photo, a signature, two fingerprints, and other citizen data. This technology was developed in 2000 in order to enhance the safety of the Brazilian ID cards.
By the end of 2005, the Brazilian government started the development of its new passport. The new documents started to be released by the beginning of 2007, in Brasilia. The new passport included several security features, like Laser perforation, UV hidden symbols, security layer over variable data and etc. Brazilian citizens will have their signature, photo, and 10 rolled fingerprints collected during passport requests. All of the data is planned to be stored in ICAO E-passport standard. This allows for contactless electronic reading of the passport content and Citizens ID verification since fingerprint templates and token facial images will be available for automatic recognition.
Canada
Canada has begun research into the use of biometric technology in the area of border security and immigration (Center for Security Sciences, Public Security Technical Program, Biometrics Community of Practice). At least one program, the NEXUS program operated jointly by the Canada Border Services AgencyCanada Border Services Agency
The Canada Border Services Agency is a federal law enforcement agency that is responsible for border enforcement, immigration enforcement and customs services....
and U.S. Customs and Border Protection
U.S. Customs and Border Protection
U.S. Customs and Border Protection is a federal law enforcement agency of the United States Department of Homeland Security charged with regulating and facilitating international trade, collecting import duties, and enforcing U.S. regulations, including trade, customs and immigration. CBP is the...
, is already operational. It is a functioning example of biometric technology, specifically "iris recognition biometric technology" used for border control and security for air travellers. Canada is also the home for the world's biggest biometric access control company called Bioscrypt Inc.
Bioscrypt Inc.
Bioscrypt Inc. is a biometrics research, development and manufacturing company. It provides fingerprint IP readers for physical access control systems, Facial recognition system readers for contactless access control authentication and OEM fingerprint modules for embedded applications.Bioscrypt is...
.
Gambia
The Gambia Biometric Identification System (GAMBIS) allowed for the issuance of Gambia's first biometric identity documents in July 2009. An individual's data, including their biometric information (thumbprints) is captured in the database. A National Identification Number (NIN), unique to each applicant applying for a card, is issued to the applicant. Biometric documents issued for Gambia include national identity cards, residential permits, non-Gambian ID cards and driver licenses.Germany
The biometrics market in Germany will experience enormous growth until the year 2009. "The market size will increase from approximately 120 million € (2004) to 377 million €" (2009). "The federal government will be a major contributor to this development". In particular, the biometric procedures of fingerprint and facial recognition can profit from the government project.In May 2005 the German Upper House of Parliament approved the implementation of the ePass, a passport issued to all German citizens which contain biometric technology. The ePass has been in circulation since November 2005, and contains a chip that holds a digital photograph and one fingerprint from each hand, usually of the index fingers, though others may be used if these fingers are missing or have extremely distorted prints. "A third biometric identifier – iris scans – could be added at a later stage".
An increase in the prevalence of biometric technology in Germany is an effort to not only keep citizens safe within German borders but also to comply with the current US deadline for visa-waiver countries to introduce biometric passports. In addition to producing biometric passports for German citizens, the German government has put in place new requirements for visitors to apply for visas within the country. "Only applicants for long-term visas, which allow more than three months' residence, will be affected by the planned biometric registration program. The new work visas will also include fingerprinting, iris scanning, and digital photos".
Germany is also one of the first countries to implement biometric technology at the Olympic Games to protect German athletes. "The Olympic Games is always a diplomatically tense affair and previous events have been rocked by terrorist attacks—most notably when Germany last held the Games in Munich in 1972 and 11 Israeli athletes were killed".
Biometric technology was first used at the Olympic Summer Games in Athens, Greece in 2004. "On registering with the scheme, accredited visitors will receive an ID card containing their fingerprint biometrics data that will enable them to access the 'German House'. Accredited visitors will include athletes, coaching staff, team management and members of the media".
As a protest against the increasing use of biometric data, the influential hacker
Hacker (computer security)
In computer security and everyday language, a hacker is someone who breaks into computers and computer networks. Hackers may be motivated by a multitude of reasons, including profit, protest, or because of the challenge...
group Chaos Computer Club
Chaos Computer Club
The Chaos Computer Club is an organization of hackers. The CCC is based in Germany and other German-speaking countries.The CCC describes itself as "a galactic community of life forms, independent of age, sex, race or societal orientation, which strives across borders for freedom of...
published a fingerprint
Fingerprint
A fingerprint in its narrow sense is an impression left by the friction ridges of a human finger. In a wider use of the term, fingerprints are the traces of an impression from the friction ridges of any part of a human hand. A print from the foot can also leave an impression of friction ridges...
of German Minister of the Interior
Federal Ministry of the Interior (Germany)
The Federal Ministry of the Interior is a ministry of the German federal government. Its main office is in Berlin, with a secondary seat in Bonn. The current minister of the interior is Dr...
Wolfgang Schäuble
Wolfgang Schäuble
Wolfgang Schäuble is a German politician of the Christian Democratic Union , currently serving as the Federal Minister of Finance in the Second Cabinet Merkel....
in the March 2008 edition of its magazine Datenschleuder. The magazine also included the fingerprint on a film that readers could use to fool fingerprint readers.
India
IndiaIndia
India , officially the Republic of India , is a country in South Asia. It is the seventh-largest country by geographical area, the second-most populous country with over 1.2 billion people, and the most populous democracy in the world...
is undertaking an ambitious mega project to provide a unique identification number to each of its 1.25 billion people. The Identification number will be stored in central databases. consisting the biometric information of the individual. If implemented, this would be the biggest implementation of the Biometrics in the world. India's Home Minister, P Chidambaram, described the process as "the biggest exercise... since humankind came into existence". The government will then use the information to issue identity cards. Officials in India will spend one year classifying India's population according to demographics indicators. The physical count began on February 2011. See Unique Identification Authority of India
Unique Identification Authority of India
The Unique Identification Authority of India , is an agency of the Government of India responsible for implementing the AADHAAR scheme, a unique identification project. It was established in February 2009, and will own and operate the Unique Identification Number database...
for more information.
Iraq
Biometrics are being used extensively in Iraq to catalogue as many Iraqis as possible providing Iraqis with a verifiable identification card, immune to forgery. During account creation, the collected biometrics information is logged into a central database which then allows a user profile to be created. Even if an Iraqi has lost their ID card, their identification can be found and verified by using their unique biometric information. Additional information can also be added to each account record, such as individual personal history.Israel
The Israeli government has passed a billBiometric Database Law (Israel)
The Biometric Database Law Is an Israeli Law which the Knesset passed in December 2009, determining that fingerprints and facial contours would be collected from all Israeli residents, that the collected data would be integrated onto the Israeli digital identity cards and digital...
calling for the creation of a biometric database of all Israeli residents; the database will contain their fingerprints and facial contours. Upon enrolling, a resident would be issued a new form of an identification card containing these biometrics. The law is currently in its trial period, during which enrollment is optional; pending on successful trial, enrollment would be mandatory for all residents.
Opponents of the proposed law, including prominent Israeli scientists and security experts, warned that the existence of such a database could damage both civil liberties and state security, because any leaks could be used by criminals or hostile individuals against Israeli residents.
Italy
Italy has standardized protocols in use to police forces. Specialist and University Faculty *Enrico Manfredi d'Angrogna Luserna v. Staufen Rome University Tor Vergata - Siena UniversityNetherlands
Starting 21 September 2009, all new Dutch passports and ID cards must include the holder's fingerprints. Since 26 August 2006, Dutch passports have included an electronic chip containing the personal details of the holder and a digitised passport photograph. The chip holds following data: your name (first name(s) and surname); the document number; your nationality, date of birth and sex; the expiry date; the country of issue; and your personal ID number (Dutch tax and social security (SoFi) number).Recent requirements for passport photographs
Since 28 August 2006, under EU regulation '2252/2004' all EU member states have been obliged to include a digital image of the holder's passport photograph.New Zealand
SmartGate was launched by the New Zealand government at Auckland International Airport on Thursday 3 December 2009. The program is available at Auckland, Wellington and Christchurch international airports for arriving travellers, and also for travellers departing from Auckland (with plans to extend the program for departures from Wellington and Christchurch by mid-2011).The kiosk and gate system will allow all New Zealand and Australian electronic passport holders over 18 to clear passport control without needing to have their identity checked by a Customs officer. The system uses "advanced facial software" which "compares your face with the digital copy of your photo in your ePassport chip".
Deputy comptroller of customs John Secker said SmartGate represented probably the biggest single development in border processing in New Zealand in the past two decades.
People will have a choice whether they want to use the system or go through normal passport control.
United Kingdom
Fingerprint scanners used in some schools to facilitate the subtraction of funds from an account financed by parents for the payment of school dinners. By using such a system nutritional reports can be produced for parents to surveil a child's intake. This has raised questions from liberty groups as taking away the liberty of choice from the youth of society. Other concerns arise from the possibility of data leaking from the providers of school meals to interest groups that provide health services such as the NHS and insurance groups that may end up having a detrimental effect on the ability of individuals to enjoy equality of access to services.United States
Starting in 2005, US passports with facial (image-based) biometric data were scheduled to be produced. Privacy activists in many countries have criticized the technology's use for the potential harm to civil liberties, privacy, and the risk of identity theft. Currently, there is some apprehension in the United States (and the European Union) that the information can be "skimmed" and identify people's citizenship remotely for criminal intent, such as kidnapping.The US Department of Defense (DoD) Common Access Card
Common Access Card
The Common Access Card is a United States Department of Defense smart card issued as standard identification for active-duty military personnel, reserve personnel, civilian employees, other non-DoD government employees, state employees of the National Guard, and eligible contractor personnel.The...
, is an ID card issued to all US Service personnel and contractors on US Military sites. This card contains biometric data and digitized photographs. It also has laser-etched photographs and holograms to add security and reduce the risk of falsification. There have been over 10 million of these cards issued.
According to Jim Wayman, director of the National Biometric Test Center at San Jose State University
San José State University
San Jose State University is a public university located in San Jose, California, United States...
, Walt Disney World
Walt Disney World Resort
Walt Disney World Resort , is the world's most-visited entertaimental resort. Located in Lake Buena Vista, Florida ; approximately southwest of Orlando, Florida, United States, the resort covers an area of and includes four theme parks, two water parks, 23 on-site themed resort hotels Walt...
is the nation's largest single commercial application of biometrics. However, the US-VISIT program will very soon surpass Walt Disney World for biometrics deployment.
The United States (US) and European Union (EU) are proposing new methods for border crossing procedures utilizing biometrics. Employing biometrically enabled travel documents will increase security and expedite travel for legitimate travelers.
NEXUS
Nexus
-Fiction:* Nexus, the final novel in The Rosy Crucifixion trilogy by Henry Miller* The Nexus, the central plot element in the film Star Trek Generations* Nexus: The Jupiter Incident, a 2004 science fiction themed real-time tactics computer game...
is a joint Canada-United States program operated by the Canada Border Services Agency
Canada Border Services Agency
The Canada Border Services Agency is a federal law enforcement agency that is responsible for border enforcement, immigration enforcement and customs services....
and U.S. Customs and Border Protection
U.S. Customs and Border Protection
U.S. Customs and Border Protection is a federal law enforcement agency of the United States Department of Homeland Security charged with regulating and facilitating international trade, collecting import duties, and enforcing U.S. regulations, including trade, customs and immigration. CBP is the...
. It is designed to expedite travel cross the US-Canada border and makes use of biometric authentication technology, specifically "iris recognition biometric technology". It permits pre-approved members of the program to use self-serve kiosks at airports, reserved lanes at land crossings, or by phoning border officials when entering by water.
In popular culture
- The 2002 film Minority ReportMinority Report (film)Minority Report is a 2002 American neo-noir science fiction film directed by Steven Spielberg and loosely based on the short story "The Minority Report" by Philip K. Dick. It is set primarily in Washington, D.C...
features extensive use of casual Iris/Retina scanning techniques for both personal Identification and Point Of Sale transaction purposes. The main character changes his official Identity by having his eyes transplanted, and later accesses a security system using one of the removed eyes.
- The movie GattacaGattacaGattaca is a 1997 science fiction film written and directed by Andrew Niccol. It stars Ethan Hawke, Uma Thurman and Jude Law with supporting roles played by Loren Dean, Ernest Borgnine, Gore Vidal and Alan Arkin....
portrays a society in which there are two classes of people: those genetically engineered to be superior (termed "Valid") and the inferior natural humans ("Invalid"). People considered "Valid" have greater privileges, and access to areas restricted to such persons is controlled by automated biometric scanners similar in appearance to fingerprint scanners, but which prick the finger and sample DNA from the resulting blood droplet
- The television program MythBustersMythBustersMythBusters is a science entertainment TV program created and produced by Beyond Television Productions for the Discovery Channel. The series is screened by numerous international broadcasters, including Discovery Channel Australia, Discovery Channel Latin America, Discovery Channel Canada, Quest...
attempted to break into a commercial security door equipped with fingerprint authentication as well as a personal laptop so equipped. While the laptop's system proved more difficult to bypass, the advanced commercial security door with "live" sensing was fooled with a printed scan of a fingerprint after it had been licked, as well as by a photocopy of a fingerprint.
- In Demolition ManDemolition Man (film)Demolition Man is a 1993 American, science fiction action film directed by Marco Brambilla, and starring Sylvester Stallone and Wesley Snipes. Sandra Bullock, Nigel Hawthorne, and Denis Leary co-star....
the character Simon Phoenix cuts out a living victim's eye in order to open a locked door which is fitted with iris scanning. A similar plot element was used in Angels & Demons (2009) when an assassin gains access to a top secret CERNCERNThe European Organization for Nuclear Research , known as CERN , is an international organization whose purpose is to operate the world's largest particle physics laboratory, which is situated in the northwest suburbs of Geneva on the Franco–Swiss border...
facility using a physicist's eye. Unfortunately, both of these examples are misleading to the audience since the methods depicted for enucleation (removal of an eye) from a corpse would not be a viable way to defeat such a system.
See also
- Access controlAccess controlAccess control refers to exerting control over who can interact with a resource. Often but not always, this involves an authority, who does the controlling. The resource can be a given building, group of buildings, or computer-based information system...
- AssureSignAssureSignAssureSign is an electronic signature software solution that can be deployed as a Software-as-a-Service application or installed on customer premise...
- AFISAutomated Fingerprint Identification SystemAutomated fingerprint identification is the process of automatically matching one or many unknown fingerprints against a database of known and unknown prints...
- BioAPIBioAPIBioAPI 'is a key part of the International Standards that support systems that perform biometric enrollment and verification...
- Biometric passportBiometric passportA biometric passport, also known as an e-passport or ePassport, is a combined paper and electronic passport that contains biometric information that can be used to authenticate the identity of travelers...
- Biometrics in schoolsBiometrics in schoolsBiometrics in schools have been used worldwide since the early first decade of the 21st century to address truancy, to replace library cards, or to charge for meals...
- BioSlimDiskBioSlimDiskBioSlimDisk is the world's first biometric USB storage device.-Signature:The biometric USB hardware is encryption coupled with dual fingerprint authentication methodology to prevent crackers bypassing the encryption...
- British biometric national identity cardBritish national identity cardThe Identity Cards Act 2006 was an Act of the Parliament of the United Kingdom. It provided for National Identity Cards, a personal identification document and European Union travel document, linked to a database known as the National Identity Register .The introduction of the scheme was much...
- Facial recognition systemFacial recognition systemA facial recognition system is a computer application for automatically identifying or verifying a person from a digital image or a video frame from a video source...
- Fingerprint recognition
- Government databases
- International Identity FederationInternational Identity FederationThe International Identity Federation was formed in Scotland during 2006. IDFed provides a web-based solution to the problem of identification of injured or distressed travellers. Members are issued with a unique number embossed onto an identity tag or bracelet...
- Iris recognitionIris recognitionIris recognition is an automated method of biometric identification that uses mathematical pattern-recognition techniques on video images of the irides of an individual's eyes, whose complex random patterns are unique and can be seen from some distance....
- Private biometricsPrivate biometricsA form of biometrics, also called Biometric Encryption or BioCryptics, in which the prover is protected against the misuse of template data by a dishonest verifier....
- Retinal scanRetinal scanA retinal scan is a biometric technique that uses the unique patterns on a person's retina to identify them. It is not to be confused with another ocular-based technology, iris recognition.-Introduction:...
- Speaker recognitionSpeaker recognitionSpeaker recognition is the computing task of validating a user's claimed identity using characteristics extracted from their voices .There is a difference between speaker recognition and speech recognition . These two terms are frequently confused, as is voice recognition...
- SurveillanceSurveillanceSurveillance is the monitoring of the behavior, activities, or other changing information, usually of people. It is sometimes done in a surreptitious manner...
- Vein matchingVein matchingVein matching, also called vascular technology, is a technique of biometric identification through the analysis of the patterns of blood vessels visible from the surface of the skin...
- Voice analysisVoice analysisVoice analysis is the study of speech sounds for purposes other than linguistic content, such as in speech recognition. Such studies include mostly medical analysis of the voice i.e. phoniatrics, but also speaker identification...
Further reading
- White Paper - Hardware Obsolescence Management in the Biometrics Industry; Reducing Costs by Enhancing the Flexibility of Biometric Solutions. Published by Aware, Inc., May 2010.
- Biomtrics Institute Privacy Code, September 2006
- Biometric Vulnerability Assessment Framework, Published by the Biometrics Institute, 2007-2011
- White Paper - Identification Flats: A Revolution in Fingerprint Biometrics. Published by Aware, Inc., March 2009.
- TechCast Article Series, Vivian Chu and Gayathri Rajendran, GWU, Use of Biometrics.
- Delac, K., Grgic, M. (2004). A Survey of Biometric Recognition Methods.
- Biometric Technology Application Manual. Published by the National Biometric Security Project (NBSP), the BTAM is a comprehensive reference manual on biometric technology applications.
- "Fingerprints Pay For School Lunch." (2001). Retrieved 2008-03-02. http://www.cbsnews.com/stories/2001/01/24/national/main266789.shtml
- "Germany to phase-in biometric passports from November 2005". (2005). E-Government News. Retrieved 2006-06-11. http://ec.europa.eu/idabc/en/document/4338/194
- Oezcan, V. (2003). "Germany Weighs Biometric Registration Options for Visa Applicants", Humboldt University Berlin. Retrieved 2006-06-11.
- Ulrich Hottelet: Hidden champion - Biometrics between boom and big brother, German Times, January 2007

