
Access control
Encyclopedia
Access control refers to exerting control over who can interact with a resource. Often but not always, this involves an authority, who does the controlling. The resource can be a given building, group of buildings, or computer-based information system. But it can also refer to a restroom stall where access is controlled by using a coin to open the door.
Access control is, in reality, an everyday phenomenon
. A lock on a car
door is essentially a form of access control. A PIN
on an ATM system at a bank is another means of access control. The possession of access control is of prime importance when persons seek to secure important, confidential, or sensitive information and equipment.
Item control or electronic key management
is an area within (and possibly integrated with) an access control system which concerns the managing of possession and location of small assets or physical (mechanical) keys.
 Physical access by a person
Physical access by a person
may be allowed depending on payment, authorization, etc. Also there may be one-way traffic of people. These can be enforced by personnel such as a border guard
, a doorman
, a ticket
checker, etc., or with a device such as a turnstile
. There may be fence
s to avoid circumventing this access control. An alternative of access control in the strict sense (physically controlling access itself) is a system of checking authorized presence, see e.g. Ticket controller (transportation). A variant is exit control, e.g. of a shop (checkout
) or a country.
In physical security
, the term access control refers to the practice of restricting entrance to a property, a building, or a room to authorized persons. Physical access control can be achieved by a human (a guard, bouncer, or receptionist), through mechanical means such as locks and keys, or through technological means such as access control systems like the Access control vestibule
. Within these environments, physical key management may also be employed as a means of further managing and monitoring access to mechanically keyed areas or access to certain small assets.
Physical access control is a matter of who, where, and when. An access control system determines who is allowed to enter or exit, where they are allowed to exit or enter, and when they are allowed to enter or exit. Historically this was partially accomplished through keys and locks. When a door is locked only someone with a key can enter through the door depending on how the lock is configured. Mechanical locks and keys do not allow restriction of the key holder to specific times or dates. Mechanical locks and keys do not provide records of the key used on any specific door and the keys can be easily copied or transferred to an unauthorized person. When a mechanical key is lost or the key holder is no longer authorized to use the protected area, the locks must be re-keyed.
Electronic access control uses computers to solve the limitations of mechanical locks and keys. A wide range of credentials can be used to replace mechanical keys. The electronic access control system grants access based on the credential presented. When access is granted, the door is unlocked for a predetermined time and the transaction is recorded. When access is refused, the door remains locked and the attempted access is recorded. The system will also monitor the door and alarm if the door is forced open or held open too long after being unlocked.
The above description illustrates a single factor transaction. Credentials can be passed around, thus subverting the access control list. For example, Alice has access rights to the server room
but Bob does not. Alice either gives Bob her credential or Bob takes it; he now has access to the server room. To prevent this, two-factor authentication
can be used. In a two factor transaction, the presented credential and a second factor are needed for access to be granted; another factor can be a PIN, a second credential, operator intervention, or a biometric input.
There are three types (factors) of authenticating information:
Passwords are a common means of verifying a user's identity before access is given to information systems. In addition, a fourth factor of authentication is now recognized: someone you know, where another person who knows you can provide a human element of authentication in situations where systems have been set up to allow for such scenarios. For example, a user may have their password, but have forgotten their smart card. In such a scenario, if the user is known to designated cohorts, the cohorts may provide their smart card and password in combination with the extant factor of the user in question and thus provide two factors for the user with missing credential, and three factors overall to allow access.
), something you are (such as a biometric feature) or some combination of these items. The typical credential is an access card, key fob, or other key. There are many card technologies including magnetic stripe, bar code, Wiegand, 125 kHz proximity, 26 bit card-swipe, contact smart cards, and contactless smart card
s. Also available are key-fobs which are more compact than ID cards and attach to a key ring. Typical biometric technologies include fingerprint, facial recognition, iris recognition, retinal scan, voice, and hand geometry.
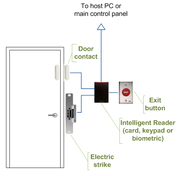
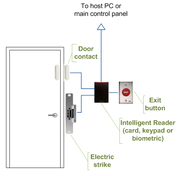
, turnstile, parking gate, elevator, or other physical barrier where granting access can be electronically controlled. Typically the access point is a door. An electronic access control door can contain several elements. At its most basic there is a stand-alone electric lock. The lock is unlocked by an operator with a switch. To automate this, operator intervention is replaced by a reader. The reader could be a keypad where a code is entered, it could be a card reader
, or it could be a biometric reader. Readers do not usually make an access decision but send a card number to an access control panel that verifies the number against an access list. To monitor the door position a magnetic door switch is used. In concept the door switch is not unlike those on refrigerators or car doors. Generally only entry is controlled and exit is uncontrolled. In cases where exit is also controlled a second reader is used on the opposite side of the door. In cases where exit is not controlled, free exit, a device called a request-to-exit (RTE) is used. Request-to-exit devices can be a push-button or a motion detector. When the button is pushed or the motion detector detects motion at the door, the door alarm is temporarily ignored while the door is opened. Exiting a door without having to electrically unlock the door is called mechanical free egress. This is an important safety feature. In cases where the lock must be electrically unlocked on exit, the request-to-exit device also unlocks the door.

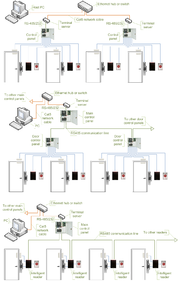
 Access control decisions are made by comparing the credential to an access control list. This lookup can be done by a host or server, by an access control panel, or by a reader. The development of access control systems has seen a steady push of the lookup out from a central host to the edge of the system, or the reader. The predominate topology circa 2009 is hub and spoke with a control panel as the hub and the readers as the spokes. The lookup and control functions are by the control panel. The spokes communicate through a serial connection; usually RS485. Some manufactures are pushing the decision making to the edge by placing a controller at the door. The controllers are IP enabled and connect to a host and database using standard networks.
Access control decisions are made by comparing the credential to an access control list. This lookup can be done by a host or server, by an access control panel, or by a reader. The development of access control systems has seen a steady push of the lookup out from a central host to the edge of the system, or the reader. The predominate topology circa 2009 is hub and spoke with a control panel as the hub and the readers as the spokes. The lookup and control functions are by the control panel. The spokes communicate through a serial connection; usually RS485. Some manufactures are pushing the decision making to the edge by placing a controller at the door. The controllers are IP enabled and connect to a host and database using standard networks.
Some readers may have additional features such as LCD and function buttons for data collection purposes (i.e. clock-in/clock-out events for attendance reports), camera/speaker/microphone for intercom, and smart card read/write support.
Access control readers may also be classified by the type of identification technology
.
 1. Serial controllers. Controllers are connected to a host PC via a serial RS-485 communication line (or via 20mA current loop
1. Serial controllers. Controllers are connected to a host PC via a serial RS-485 communication line (or via 20mA current loop
in some older systems). External RS-232/485 converters or internal RS-485 cards have to be installed as standard PCs do not have RS-485 communication ports.
Advantages:
Disadvantages:
 2. Serial main and sub-controllers. All door hardware is connected to sub-controllers (a.k.a. door controllers or door interfaces). Sub-controllers usually do not make access decisions, and forward all requests to the main controllers. Main controllers usually support from 16 to 32 sub-controllers.
2. Serial main and sub-controllers. All door hardware is connected to sub-controllers (a.k.a. door controllers or door interfaces). Sub-controllers usually do not make access decisions, and forward all requests to the main controllers. Main controllers usually support from 16 to 32 sub-controllers.
Advantages:
Disadvantages:
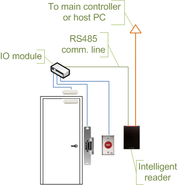
 3. Serial main controllers & intelligent readers. All door hardware is connected directly to intelligent or semi-intelligent readers. Readers usually do not make access decisions, and forward all requests to the main controller. Only if the connection to the main controller is unavailable, the readers use their internal database to make access decisions and record events. Semi-intelligent reader that have no database and cannot function without the main controller should be used only in areas that do not require high security. Main controllers usually support from 16 to 64 readers. All advantages and disadvantages are the same as the ones listed in the second paragraph.
3. Serial main controllers & intelligent readers. All door hardware is connected directly to intelligent or semi-intelligent readers. Readers usually do not make access decisions, and forward all requests to the main controller. Only if the connection to the main controller is unavailable, the readers use their internal database to make access decisions and record events. Semi-intelligent reader that have no database and cannot function without the main controller should be used only in areas that do not require high security. Main controllers usually support from 16 to 64 readers. All advantages and disadvantages are the same as the ones listed in the second paragraph.
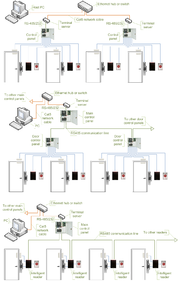 4. Serial controllers with terminal servers. In spite of the rapid development and increasing use of computer networks, access control manufacturers remained conservative and did not rush to introduce network-enabled products. When pressed for solutions with network connectivity, many chose the option requiring less efforts: addition of a terminal server
4. Serial controllers with terminal servers. In spite of the rapid development and increasing use of computer networks, access control manufacturers remained conservative and did not rush to introduce network-enabled products. When pressed for solutions with network connectivity, many chose the option requiring less efforts: addition of a terminal server
, a device that converts serial data for transmission via LAN or WAN.
Advantages:
Disadvantages:
All RS-485-related advantages and disadvantages also apply.
 5. Network-enabled main controllers. The topology is nearly the same as described in the second and third paragraphs. The same advantages and disadvantages apply, but the on-board network interface offers a couple valuable improvements. Transmission of configuration and users to the main controllers is faster and may be done in parallel. This makes the system more responsive and does not interrupt normal operations. No special hardware is required in order to achieve redundant host PC setup: in case the primary host PC fails, the secondary host PC may start polling network controllers. The disadvantages introduced by terminal servers (listed in the fourth paragraph) are also eliminated.
5. Network-enabled main controllers. The topology is nearly the same as described in the second and third paragraphs. The same advantages and disadvantages apply, but the on-board network interface offers a couple valuable improvements. Transmission of configuration and users to the main controllers is faster and may be done in parallel. This makes the system more responsive and does not interrupt normal operations. No special hardware is required in order to achieve redundant host PC setup: in case the primary host PC fails, the secondary host PC may start polling network controllers. The disadvantages introduced by terminal servers (listed in the fourth paragraph) are also eliminated.
 6. IP controllers
6. IP controllers
. Controllers are connected to a host PC via Ethernet LAN or WAN.
Advantages:
Disadvantages:
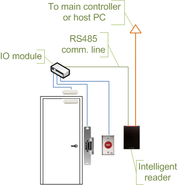
 7. IP reader
7. IP reader
s. Readers are connected to a host PC via Ethernet LAN or WAN.
Advantages:
Disadvantages:
The advantages and disadvantages of IP controllers apply to the IP readers as well.
 The most common security risk of intrusion of an access control system is simply following a legitimate user through a door. Often the legitimate user will hold the door for the intruder. This risk can be minimized through security awareness training of the user population or more active means such as turnstiles. In very high security applications this risk is minimized by using a sally port, sometimes called a security vestibule or mantrap where operator intervention is required presumably to assure valid identification.
The most common security risk of intrusion of an access control system is simply following a legitimate user through a door. Often the legitimate user will hold the door for the intruder. This risk can be minimized through security awareness training of the user population or more active means such as turnstiles. In very high security applications this risk is minimized by using a sally port, sometimes called a security vestibule or mantrap where operator intervention is required presumably to assure valid identification.
The second most common risk is from levering the door open. This is surprisingly simple and effective on most doors. The lever could be as small as a screw driver or big as a crow bar. Fully implemented access control systems include forced door monitoring alarms. These vary in effectiveness usually failing from high false positive alarms, poor database configuration, or lack of active intrusion monitoring.
Similar to levering is crashing through cheap partition walls. In shared tenant spaces the divisional wall is a vulnerability. Along the same lines is breaking sidelights.
Spoofing locking hardware is fairly simple and more elegant than levering. A strong magnet can operate the solenoid controlling bolts in electric locking hardware. Motor locks, more prevalent in Europe than in the US, are also susceptible to this attack using a donut shaped magnet. It is also possible to manipulate the power to the lock either by removing or adding current.
Access cards themselves have proven vulnerable to sophisticated attacks. Enterprising hackers have built portable readers that capture the card number from a user’s proximity card. The hacker simply walks by the user, reads the card, and then presents the number to a reader securing the door. This is possible because card numbers are sent in the clear, no encryption being used.
Finally, most electric locking hardware still have mechanical keys as a fail-over. Mechanical key locks are vulnerable to bumping
.
.
, access control includes authentication
, authorization
and audit
. It also includes measures such as physical devices, including biometric scans and metal lock
s, hidden paths, digital signature
s, encryption
, social barriers, and monitoring by humans and automated systems.
In any access control model, the entities that can perform actions in the system are called subjects, and the entities representing resources to which access may need to be controlled are called objects (see also Access Control Matrix
). Subjects and objects should both be considered as software entities, rather than as human users: any human user can only have an effect on the system via the software entities that they control.
Although some systems equate subjects with user IDs, so that all processes started by a user by default have the same authority, this level of control is not fine-grained enough to satisfy the Principle of least privilege
, and arguably is responsible for the prevalence of malware
in such systems (see computer insecurity
).
In some models, for example the object-capability model
, any software entity can potentially act as both a subject and object.
Access control models used by current systems tend to fall into one of two classes: those based on capabilities
and those based on access control lists (ACLs). In a capability-based model, holding an unforgettable reference or capability to an object provides access to the object (roughly analogous to how possession of your house key grants you access to your house); access is conveyed to another party by transmitting such a capability over a secure channel. In an ACL-based model, a subject's access to an object depends on whether its identity is on a list associated with the object (roughly analogous to how a bouncer at a private party would check your ID to see if your name is on the guest list); access is conveyed by editing the list. (Different ACL systems have a variety of different conventions regarding who or what is responsible for editing the list and how it is edited.)
Both capability-based and ACL-based models have mechanisms to allow access rights to be granted to all members of a group of subjects (often the group is itself modeled as a subject).
Access control systems provide the essential services of identification and authentication (I&A), authorization, and accountability where:
Authenticators are commonly based on at least one of the following four factors:
Most modern operating systems define sets of permissions that are variations or extensions of three basic types of access:
These rights and permissions are implemented differently in systems based on discretionary access control
(DAC) and mandatory access control
(MAC).
If no one is regularly reviewing your logs and they are not maintained in a secure and consistent manner, they may not be admissible as evidence.
Many systems can generate automated reports based on certain predefined criteria or thresholds, known as clipping levels. For example, a clipping level may be set to generate a report for the following:
These reports help a system administrator or security administrator to more easily identify possible break-in attempts.
Access control models are sometimes categorized as either discretionary or non-discretionary. The three most widely recognized models are Discretionary Access Control (DAC), Mandatory Access Control (MAC), and Role Based Access Control (RBAC). MAC and RBAC are both non-discretionary.
(extensible access control markup language).
(DAC) is an access policy determined by the owner of an object. The owner decides who is allowed to access the object and what privileges they have.
Two important concepts in DAC are
Access controls may be discretionary in ACL-based
or capability-based
access control systems. (In capability-based systems, there is usually no explicit concept of 'owner', but the creator of an object has a similar degree of control over its access policy.)
refers to allowing access to a resource if and only if rules exist that allow a given user to access the resource. It is difficult to manage but its use is usually justified when used to protect highly sensitive information. Examples include certain government and military information. Management is often simplified (over what can be required) if the information can be protected using hierarchical access control, or by implementing sensitivity labels. What makes the method "mandatory" is the use of either rules or sensitivity labels.
Two methods are commonly used for applying mandatory access control:
Few systems implement MAC; XTS-400
and SELinux are examples of systems that do. The computer system at the company in the film Tron
is an example from the prior century.
(RBAC) is an access policy determined by the system, not the owner. RBAC is used in
commercial applications and also in military systems, where multi-level security requirements may also exist.
RBAC differs from DAC in that DAC allows users to control access to their resources, while in RBAC, access is controlled
at the system level, outside of the user's control. Although RBAC is non-discretionary, it can be distinguished from
MAC primarily in the way permissions are handled. MAC controls read and write permissions based on a user's clearance level and additional labels. RBAC controls collections of permissions that may include complex operations
such as an e-commerce transaction, or may be as simple as read or write. A role in RBAC can be viewed as a set of
permissions.
Three primary rules are defined for RBAC:
Additional constraints may be applied as well, and roles can be combined in a hierarchy where higher-level roles subsume permissions owned by sub-roles.
Most IT vendors offer RBAC in one or more products.
, the term access control is defined in U.S. Federal Standard 1037C
with the following meanings:
This definition depends on several other technical terms from Federal Standard 1037C.
, access control to restrict access to systems ("authorization
") or to track or monitor behavior within systems ("accountability
") is an implementation feature of using trusted systems for security
or social control
.
Access control is, in reality, an everyday phenomenon
Phenomenon
A phenomenon , plural phenomena, is any observable occurrence. Phenomena are often, but not always, understood as 'appearances' or 'experiences'...
. A lock on a car
Čar
Čar is a village in the municipality of Bujanovac, Serbia. According to the 2002 census, the town has a population of 296 people.-References:...
door is essentially a form of access control. A PIN
Personal identification number
A personal identification number is a secret numeric password shared between a user and a system that can be used to authenticate the user to the system. Typically, the user is required to provide a non-confidential user identifier or token and a confidential PIN to gain access to the system...
on an ATM system at a bank is another means of access control. The possession of access control is of prime importance when persons seek to secure important, confidential, or sensitive information and equipment.
Item control or electronic key management
Electronic key management
Electronic key management is an area of access control within the broader category of security. Typically, physical mechanical keys are managed electronically by a system which controls key access and also creates reports and generates alarms...
is an area within (and possibly integrated with) an access control system which concerns the managing of possession and location of small assets or physical (mechanical) keys.
Physical access

Admission to an event or establishment
Admission to a journey or other event or establishment may be subject to paying an entrance fee / buying a ticket. A pass may give admittance without a ticket for a given time period, or give the right to obtain free tickets. A discount pass allows buying tickets at a reduced price...
may be allowed depending on payment, authorization, etc. Also there may be one-way traffic of people. These can be enforced by personnel such as a border guard
Border guard
The border guard, frontier guard, border patrol, border police, or frontier police of a country is a national security agency that performs border control, i.e., enforces the security of the country's national borders....
, a doorman
Bouncer (doorman)
A bouncer is an informal term for a type of security guard employed at venues such as bars, nightclubs or concerts to provide security, check legal age, and refuse entry to a venue based on criteria such as intoxication, aggressive behavior, or attractiveness...
, a ticket
Ticket (admission)
A ticket is a voucher that indicates that one has paid for admission to an event or establishment such as a theatre, movie theater, amusement park, zoo, museum, concert, or other attraction, or permission to travel on a vehicle such as an airliner, train, bus, or boat, typically because one has...
checker, etc., or with a device such as a turnstile
Turnstile
A turnstile, also called a baffle gate, is a form of gate which allows one person to pass at a time. It can also be made so as to enforce one-way traffic of people, and in addition, it can restrict passage only to people who insert a coin, a ticket, a pass, or similar...
. There may be fence
Fence
A fence is a freestanding structure designed to restrict or prevent movement across a boundary. It is generally distinguished from a wall by the lightness of its construction: a wall is usually restricted to such barriers made from solid brick or concrete, blocking vision as well as passage .Fences...
s to avoid circumventing this access control. An alternative of access control in the strict sense (physically controlling access itself) is a system of checking authorized presence, see e.g. Ticket controller (transportation). A variant is exit control, e.g. of a shop (checkout
Checkout
Checkout can have the following meanings:*a point of sale terminal*in information management, it means blocking a file for editing; see Revision control*Checkout , a comedy...
) or a country.
In physical security
Physical security
Physical security describes measures that are designed to deny access to unauthorized personnel from physically accessing a building, facility, resource, or stored information; and guidance on how to design structures to resist potentially hostile acts...
, the term access control refers to the practice of restricting entrance to a property, a building, or a room to authorized persons. Physical access control can be achieved by a human (a guard, bouncer, or receptionist), through mechanical means such as locks and keys, or through technological means such as access control systems like the Access control vestibule
Access control vestibule
The Access Control Vestibule is a security screening system for the detection of individuals carrying weapons into any facility without authorization, therefore minimizing the possibility of an armed takeover. The ACV is composed of an aluminum frame, separate entrance and exit doors, a metal...
. Within these environments, physical key management may also be employed as a means of further managing and monitoring access to mechanically keyed areas or access to certain small assets.
Physical access control is a matter of who, where, and when. An access control system determines who is allowed to enter or exit, where they are allowed to exit or enter, and when they are allowed to enter or exit. Historically this was partially accomplished through keys and locks. When a door is locked only someone with a key can enter through the door depending on how the lock is configured. Mechanical locks and keys do not allow restriction of the key holder to specific times or dates. Mechanical locks and keys do not provide records of the key used on any specific door and the keys can be easily copied or transferred to an unauthorized person. When a mechanical key is lost or the key holder is no longer authorized to use the protected area, the locks must be re-keyed.
Electronic access control uses computers to solve the limitations of mechanical locks and keys. A wide range of credentials can be used to replace mechanical keys. The electronic access control system grants access based on the credential presented. When access is granted, the door is unlocked for a predetermined time and the transaction is recorded. When access is refused, the door remains locked and the attempted access is recorded. The system will also monitor the door and alarm if the door is forced open or held open too long after being unlocked.
Access control system operation
When a credential is presented to a reader, the reader sends the credential’s information, usually a number, to a control panel, a highly reliable processor. The control panel compares the credential's number to an access control list, grants or denies the presented request, and sends a transaction log to a database. When access is denied based on the access control list, the door remains locked. If there is a match between the credential and the access control list, the control panel operates a relay that in turn unlocks the door. The control panel also ignores a door open signal to prevent an alarm. Often the reader provides feedback, such as a flashing red LED for an access denied and a flashing green LED for an access granted.The above description illustrates a single factor transaction. Credentials can be passed around, thus subverting the access control list. For example, Alice has access rights to the server room
Server room
A server room is a room that houses mainly computer servers. In information technology circles, the term is generally used for smaller arrangements of servers; larger groups of servers are housed in data centers...
but Bob does not. Alice either gives Bob her credential or Bob takes it; he now has access to the server room. To prevent this, two-factor authentication
Two-factor authentication
Two-factor authentication is an approach to authentication which requires the presentation of two different kinds of evidence that someone is who they say they are. It is a part of the broader family of multi-factor authentication, which is a defense in depth approach to security...
can be used. In a two factor transaction, the presented credential and a second factor are needed for access to be granted; another factor can be a PIN, a second credential, operator intervention, or a biometric input.
There are three types (factors) of authenticating information:
- something the user knows, e.g. a password, pass-phrase or PIN
- something the user has, such as smart card
- something the user is, such as fingerprint, verified by biometric measurement
Passwords are a common means of verifying a user's identity before access is given to information systems. In addition, a fourth factor of authentication is now recognized: someone you know, where another person who knows you can provide a human element of authentication in situations where systems have been set up to allow for such scenarios. For example, a user may have their password, but have forgotten their smart card. In such a scenario, if the user is known to designated cohorts, the cohorts may provide their smart card and password in combination with the extant factor of the user in question and thus provide two factors for the user with missing credential, and three factors overall to allow access.
Credential
A credential is a physical/tangible object, a piece of knowledge, or a facet of a person's physical being, that enables an individual access to a given physical facility or computer-based information system. Typically, credentials can be something you know (such as number or PIN), something you have (such as an access badgeAccess badge
An access badge is a credential used to gain entry to an area having automated access control entry points. Entry points may be doors, turnstiles, parking gates or other barriers....
), something you are (such as a biometric feature) or some combination of these items. The typical credential is an access card, key fob, or other key. There are many card technologies including magnetic stripe, bar code, Wiegand, 125 kHz proximity, 26 bit card-swipe, contact smart cards, and contactless smart card
Contactless smart card
A contactless smart card is any pocket-sized card with embedded integrated circuits that can process and store data, and communicate with a terminal via radio waves. There are two broad categories of contactless smart cards. Memory cards contain non-volatile memory storage components, and perhaps...
s. Also available are key-fobs which are more compact than ID cards and attach to a key ring. Typical biometric technologies include fingerprint, facial recognition, iris recognition, retinal scan, voice, and hand geometry.
Access control system components
An access control point, which can be a doorDoor
A door is a movable structure used to open and close off an entrance, typically consisting of a panel that swings on hinges or that slides or rotates inside of a space....
, turnstile, parking gate, elevator, or other physical barrier where granting access can be electronically controlled. Typically the access point is a door. An electronic access control door can contain several elements. At its most basic there is a stand-alone electric lock. The lock is unlocked by an operator with a switch. To automate this, operator intervention is replaced by a reader. The reader could be a keypad where a code is entered, it could be a card reader
Card reader
A card reader is a data input device that reads data from a card-shaped storage medium. Historically, paper or cardboard punched cards were used throughout the first several decades of the computer industry to store information and programs for computer system, and were read by punched card readers...
, or it could be a biometric reader. Readers do not usually make an access decision but send a card number to an access control panel that verifies the number against an access list. To monitor the door position a magnetic door switch is used. In concept the door switch is not unlike those on refrigerators or car doors. Generally only entry is controlled and exit is uncontrolled. In cases where exit is also controlled a second reader is used on the opposite side of the door. In cases where exit is not controlled, free exit, a device called a request-to-exit (RTE) is used. Request-to-exit devices can be a push-button or a motion detector. When the button is pushed or the motion detector detects motion at the door, the door alarm is temporarily ignored while the door is opened. Exiting a door without having to electrically unlock the door is called mechanical free egress. This is an important safety feature. In cases where the lock must be electrically unlocked on exit, the request-to-exit device also unlocks the door.
Access control topology

Types of readers
Access control readers may be classified by functions they are able to perform:- Basic (non-intelligent) readers: simply read card number or PIN and forward it to a control panel. In case of biometric identification, such readers output ID number of a user. Typically Wiegand protocolWiegand interfaceThe Wiegand interface is a de facto wiring standard which arose from the popularity of Wiegand effect card readers in the 1980s. It is commonly used to connect a card swipe mechanism to the rest of an electronic entry system. The sensor in such a system is often a Wiegand wire based on the Wiegand...
is used for transmitting data to the control panel, but other options such as RS-232, RS-485 and Clock/Data are not uncommon. This is the most popular type of access control readers. Examples of such readers are RF Tiny by RFLOGICS, ProxPoint by HID, and P300 by Farpointe Data. - Semi-intelligent readers: have all inputs and outputs necessary to control door hardware (lock, door contact, exit button), but do not make any access decisions. When a user presents a card or enters PIN, the reader sends information to the main controller and waits for its response. If the connection to the main controller is interrupted, such readers stop working or function in a degraded mode. Usually semi-intelligent readers are connected to a control panel via an RS-485 bus. Examples of such readers are InfoProx Lite IPL200 by CEM Systems and AP-510 by Apollo.
- Intelligent readers: have all inputs and outputs necessary to control door hardware, they also have memory and processing power necessary to make access decisions independently. Same as semi-intelligent readers they are connected to a control panel via an RS-485 bus. The control panel sends configuration updates and retrieves events from the readers. Examples of such readers could be InfoProx IPO200 by CEM Systems and AP-500 by Apollo. There is also a new generation of intelligent readers referred to as "IP readerIP readerIP reader is an electronic security device designed to identify users and control entry to or exit from protected areas.-Operation:An IP reader has two features that distinguish it from other access control readers:...
s". Systems with IP readers usually do not have traditional control panels and readers communicate directly to PC that acts as a host. Examples of such readers are PowerNet IP Reader by Isonas Security Systems, ID08 by Solus has the built in webservice to make it user friendly, Edge ER40 reader by HID Global, LogLock and UNiLOCK by ASPiSYS Ltd, BioEntry Plus reader by Suprema Inc. and 4G V-Station by Bioscrypt Inc.Bioscrypt Inc.Bioscrypt Inc. is a biometrics research, development and manufacturing company. It provides fingerprint IP readers for physical access control systems, Facial recognition system readers for contactless access control authentication and OEM fingerprint modules for embedded applications.Bioscrypt is...
Some readers may have additional features such as LCD and function buttons for data collection purposes (i.e. clock-in/clock-out events for attendance reports), camera/speaker/microphone for intercom, and smart card read/write support.
Access control readers may also be classified by the type of identification technology
Card reader
A card reader is a data input device that reads data from a card-shaped storage medium. Historically, paper or cardboard punched cards were used throughout the first several decades of the computer industry to store information and programs for computer system, and were read by punched card readers...
.
Access control system topologies

Current loop
A current loop describes two different electrical signalling schemes.- Digital :For digital serial communications, a current loop is a communication interface that uses current instead of voltage for signaling...
in some older systems). External RS-232/485 converters or internal RS-485 cards have to be installed as standard PCs do not have RS-485 communication ports.
Advantages:
- RS-485 standard allows long cable runs, up to 4000 feet (1200 m)
- Relatively short response time. The maximum number of devices on an RS-485 line is limited to 32, which means that the host can frequently request status updates from each device and display events almost in real time.
- High reliability and security as the communication line is not shared with any other systems.
Disadvantages:
- RS-485 does not allow Star-type wiring unless splitters are used
- RS-485 is not well suited for transferring large amounts of data (i.e. configuration and users). The highest possible throughput is 115.2 kbit/s, but in most system it is downgraded to 56.2 kbit/s or less to increase reliability.
- RS-485 does not allow host PC to communicate with several controllers connected to the same port simultaneously. Therefore in large systems transfers of configuration and users to controllers may take a very long time and interfere with normal operations.
- Controllers cannot initiate communication in case of an alarm. The host PC acts as a master on the RS-485 communication line and controllers have to wait till they are polled.
- Special serial switches are required in order to build a redundant host PC setup.
- Separate RS-485 lines have to be installed instead of using an already existing network infrastructure.
- Cable that meets RS-485 standards is significantly more expensive than the regular Category 5 UTP network cable.
- Operation of the system is highly dependent on the host PC. In case the host PC fails, events from controllers are not retrieved and functions that required interaction between controllers (i.e. anti-passback) stop working.

Advantages:
- Work load on the host PC is significantly reduced, because it only needs to communicate with a few main controllers.
- The overall cost of the system is lower, as sub-controllers are usually simple and inexpensive devices.
- All other advantages listed in the first paragraph apply.
Disadvantages:
- Operation of the system is highly dependent on main controllers. In case one of the main controllers fails, events from its sub-controllers are not retrieved and functions that require interaction between sub controllers (i.e. anti-passback) stop working.
- Some models of sub-controllers (usually lower cost) have no memory and processing power to make access decisions independently. If the main controller fails, sub-controllers change to degraded mode in which doors are either completely locked or unlocked and no events are recorded. Such sub-controllers should be avoided or used only in areas that do not require high security.
- Main controllers tend to be expensive, therefore such topology is not very well suited for systems with multiple remote locations that have only a few doors.
- All other RS-485-related disadvantages listed in the first paragraph apply.

Terminal server
A terminal server enables organizations to connect devices with an RS-232, RS-422 or RS-485 serial interface to a local area network . Products marketed as terminal servers can be very simple devices that do not offer any security functionality, such as data encryption and user authentication...
, a device that converts serial data for transmission via LAN or WAN.
Advantages:
- Allows utilizing existing network infrastructure for connecting separate segments of the system. ABC
- Provides convenient solution in cases when installation of an RS-485 line would be difficult or impossible.
Disadvantages:
- Increases complexity of the system.
- Creates additional work for installers: usually terminal servers have to be configured independently, not through the interface of the access control software.
- Serial communication link between the controller and the terminal server acts as a bottleneck: even though the data between the host PC and the terminal server travels at the 10/100/1000Mbit/s network speed it then slows down to the serial speed of 112.5 kbit/s or less. There are also additional delays introduced in the process of conversion between serial and network data.
All RS-485-related advantages and disadvantages also apply.


IP access controller
IP access controller is an electronic security device designed to identify users and control entry to or exit from protected areas. A typical IP access controller supports 2 or 4 basic access control readers...
. Controllers are connected to a host PC via Ethernet LAN or WAN.
Advantages:
- An existing network infrastructure is fully utilized, there is no need to install new communication lines.
- There are no limitations regarding the number of controllers (32 per line in case of RS-485).
- Special RS-485 installation, termination, grounding and troubleshooting knowledge is not required.
- Communication with controllers may be done at the full network speed, which is important if transferring a lot of data (databases with thousands of users, possibly including biometric records).
- In case of an alarm controllers may initiate connection to the host PC. This ability is important in large systems because it allows to reduce network traffic caused by unnecessary polling.
- Simplifies installation of systems consisting of multiple sites separated by large distances. Basic Internet link is sufficient to establish connections to remote locations.
- Wide selection of standard network equipment is available to provide connectivity in different situations (fiber, wireless, VPN, dual path, PoE)
Disadvantages:
- The system becomes susceptible to network related problems, such as delays in case of heavy traffic and network equipment failures.
- Access controllers and workstations may become accessible to hackers if the network of the organization is not well protected. This threat may be eliminated by physically separating the access control network from the network of the organization. Also it should be noted that most IP controllers utilize either Linux platform or proprietary operating systems, which makes them more difficult to hack. Industry standard data encryption is also used.
- Maximum distance from a hub or a switch to the controller (if using a copper cable) is 100 meters (330 ft).
- Operation of the system is dependent on the host PC. In case the host PC fails, events from controllers are not retrieved and functions that require interaction between controllers (i.e. anti-passback) stop working. Some controllers, however, have peer-to-peer communication option in order to reduce dependency on the host PC.

IP reader
IP reader is an electronic security device designed to identify users and control entry to or exit from protected areas.-Operation:An IP reader has two features that distinguish it from other access control readers:...
s. Readers are connected to a host PC via Ethernet LAN or WAN.
Advantages:
- Most IP readers are PoE capable. This feature makes it very easy to provide battery backed power to the entire system, including the locks and various types of detectors (if used).
- IP readers eliminate the need for controller enclosures.
- There is no wasted capacity when using IP readers (i.e. a 4-door controller would have 25% unused capacity if it was controlling only 3 doors).
- IP reader systems scale easily: there is no need to install new main or sub-controllers.
- Failure of one IP reader does not affect any other readers in the system.
Disadvantages:
- In order to be used in high-security areas IP readers require special input/output modules to eliminate the possibility of intrusion by accessing lock and/or exit button wiring. Not all IP reader manufacturers have such modules available.
- Being more sophisticated than basic readers IP readers are also more expensive and sensitive, therefore they should not be installed outdoors in areas with harsh weather conditions or high possibility of vandalism, unless specifically designed for exterior installation. A few manufacturers make such models.
The advantages and disadvantages of IP controllers apply to the IP readers as well.
Security risks
The second most common risk is from levering the door open. This is surprisingly simple and effective on most doors. The lever could be as small as a screw driver or big as a crow bar. Fully implemented access control systems include forced door monitoring alarms. These vary in effectiveness usually failing from high false positive alarms, poor database configuration, or lack of active intrusion monitoring.
Similar to levering is crashing through cheap partition walls. In shared tenant spaces the divisional wall is a vulnerability. Along the same lines is breaking sidelights.
Spoofing locking hardware is fairly simple and more elegant than levering. A strong magnet can operate the solenoid controlling bolts in electric locking hardware. Motor locks, more prevalent in Europe than in the US, are also susceptible to this attack using a donut shaped magnet. It is also possible to manipulate the power to the lock either by removing or adding current.
Access cards themselves have proven vulnerable to sophisticated attacks. Enterprising hackers have built portable readers that capture the card number from a user’s proximity card. The hacker simply walks by the user, reads the card, and then presents the number to a reader securing the door. This is possible because card numbers are sent in the clear, no encryption being used.
Finally, most electric locking hardware still have mechanical keys as a fail-over. Mechanical key locks are vulnerable to bumping
Lock bumping
Lock bumping is a lock picking technique for opening a pin tumbler lock using a specially crafted bump key. One bump key will work for all locks of the same type.-History:A US patent first appears in 1928 by H.R. Simpson called a "rapping" or bump-key...
.
The need-to-know principle
The need to know principle can be enforced with user access controls and authorization procedures and its objective is to ensure that only authorized individuals gain access to information or systems necessary to undertake their duties. See Principle of least privilegePrinciple of least privilege
In information security, computer science, and other fields, the principle of least privilege, also known as the principle of minimal privilege or just least privilege, requires that in a particular abstraction layer of a computing environment, every module must be able to access only the...
.
Computer security
In computer securityComputer security
Computer security is a branch of computer technology known as information security as applied to computers and networks. The objective of computer security includes protection of information and property from theft, corruption, or natural disaster, while allowing the information and property to...
, access control includes authentication
Authentication
Authentication is the act of confirming the truth of an attribute of a datum or entity...
, authorization
Authorization
Authorization is the function of specifying access rights to resources, which is related to information security and computer security in general and to access control in particular. More formally, "to authorize" is to define access policy...
and audit
Audit trail
Audit trail is a sequence of steps supported by proof documenting the real processing of a transaction flow through an organization, a process or a system.....
. It also includes measures such as physical devices, including biometric scans and metal lock
Lock (device)
A lock is a mechanical or electronic fastening device that is released by a physical object or secret information , or combination of more than one of these....
s, hidden paths, digital signature
Digital signature
A digital signature or digital signature scheme is a mathematical scheme for demonstrating the authenticity of a digital message or document. A valid digital signature gives a recipient reason to believe that the message was created by a known sender, and that it was not altered in transit...
s, encryption
Encryption
In cryptography, encryption is the process of transforming information using an algorithm to make it unreadable to anyone except those possessing special knowledge, usually referred to as a key. The result of the process is encrypted information...
, social barriers, and monitoring by humans and automated systems.
In any access control model, the entities that can perform actions in the system are called subjects, and the entities representing resources to which access may need to be controlled are called objects (see also Access Control Matrix
Access Control Matrix
In computer science, an Access Control Matrix or Access Matrix is an abstract, formal security model of protection state in computer systems, that characterizes the rights of each subject with respect to every object in the system. It was first introduced by Butler W...
). Subjects and objects should both be considered as software entities, rather than as human users: any human user can only have an effect on the system via the software entities that they control.
Although some systems equate subjects with user IDs, so that all processes started by a user by default have the same authority, this level of control is not fine-grained enough to satisfy the Principle of least privilege
Principle of least privilege
In information security, computer science, and other fields, the principle of least privilege, also known as the principle of minimal privilege or just least privilege, requires that in a particular abstraction layer of a computing environment, every module must be able to access only the...
, and arguably is responsible for the prevalence of malware
Malware
Malware, short for malicious software, consists of programming that is designed to disrupt or deny operation, gather information that leads to loss of privacy or exploitation, or gain unauthorized access to system resources, or that otherwise exhibits abusive behavior...
in such systems (see computer insecurity
Computer insecurity
Computer insecurity refers to the concept that a computer system is always vulnerable to attack, and that this fact creates a constant battle between those looking to improve security, and those looking to circumvent security.-Security and systems design:...
).
In some models, for example the object-capability model
Object-capability model
The object-capability model is a computer security model based on the Actor model of computation. The name "object-capability model" is due to the idea that the capability to perform an operation can be obtained by the following combination:...
, any software entity can potentially act as both a subject and object.
Access control models used by current systems tend to fall into one of two classes: those based on capabilities
Capability-based security
Capability-based security is a concept in the design of secure computing systems, one of the existing security models. A capability is a communicable, unforgeable token of authority. It refers to a value that references an object along with an associated set of access rights...
and those based on access control lists (ACLs). In a capability-based model, holding an unforgettable reference or capability to an object provides access to the object (roughly analogous to how possession of your house key grants you access to your house); access is conveyed to another party by transmitting such a capability over a secure channel. In an ACL-based model, a subject's access to an object depends on whether its identity is on a list associated with the object (roughly analogous to how a bouncer at a private party would check your ID to see if your name is on the guest list); access is conveyed by editing the list. (Different ACL systems have a variety of different conventions regarding who or what is responsible for editing the list and how it is edited.)
Both capability-based and ACL-based models have mechanisms to allow access rights to be granted to all members of a group of subjects (often the group is itself modeled as a subject).
Access control systems provide the essential services of identification and authentication (I&A), authorization, and accountability where:
- identification and authentication determine who can log on to a system, and the association of users with the software subjects that they are able to control as a result of logging in;
- authorization determines what a subject can do;
- accountability identifies what a subject (or all subjects associated with a user) did.
Identification and authentication (I&A)
Identification and authentication (I&A) is the process of verifying that an identity is bound to the entity that makes an assertion or claim of identity. The I&A process assumes that there was an initial validation of the identity, commonly called identity proofing. Various methods of identity proofing are available ranging from in person validation using government issued identification to anonymous methods that allow the claimant to remain anonymous, but known to the system if they return. The method used for identity proofing and validation should provide an assurance level commensurate with the intended use of the identity within the system. Subsequently, the entity asserts an identity together with an authenticator as a means for validation. The only requirements for the identifier is that it must be unique within its security domain.Authenticators are commonly based on at least one of the following four factors:
- Something you know, such as a password or a personal identification number (PIN). This assumes that only the owner of the account knows the password or PIN needed to access the account.
- Something you have, such as a smart cardSmart cardA smart card, chip card, or integrated circuit card , is any pocket-sized card with embedded integrated circuits. A smart card or microprocessor cards contain volatile memory and microprocessor components. The card is made of plastic, generally polyvinyl chloride, but sometimes acrylonitrile...
or security tokenSecurity tokenA security token may be a physical device that an authorized user of computer services is given to ease authentication...
. This assumes that only the owner of the account has the necessary smart card or token needed to unlock the account. - Something you are, such as fingerprint, voice, retina, or iris characteristics.
- Where you are, for example inside or outside a company firewall, or proximity of login location to a personal GPS device.
Authorization
Authorization applies to subjects. Authorization determines what a subject can do on the system.Most modern operating systems define sets of permissions that are variations or extensions of three basic types of access:
- Read (R): The subject can
- Read file contents
- List directory contents
- Write (W): The subject can change the contents of a file or directory with the following tasks:
- Add
- Create
- Delete
- Rename
- Execute (X): If the file is a program, the subject can cause the program to be run. (In Unix systems, the 'execute' permission doubles as a 'traverse directory' permission when granted for a directory.)
These rights and permissions are implemented differently in systems based on discretionary access control
Discretionary access control
In computer security, discretionary access control is a kind of access control defined by the Trusted Computer System Evaluation Criteria "as a means of restricting access to objects based on the identity of subjects and/or groups to which they belong...
(DAC) and mandatory access control
Mandatory access control
In computer security, mandatory access control refers to a type of access control by which the operating system constrains the ability of a subject or initiator to access or generally perform some sort of operation on an object or target...
(MAC).
Accountability
Accountability uses such system components as audit trails (records) and logs to associate a subject with its actions. The information recorded should be sufficient to map the subject to a controlling user. Audit trails and logs are important for- Detecting security violations
- Re-creating security incidents
If no one is regularly reviewing your logs and they are not maintained in a secure and consistent manner, they may not be admissible as evidence.
Many systems can generate automated reports based on certain predefined criteria or thresholds, known as clipping levels. For example, a clipping level may be set to generate a report for the following:
- More than three failed logon attempts in a given period
- Any attempt to use a disabled user account
These reports help a system administrator or security administrator to more easily identify possible break-in attempts.
Access control models
Access control models are sometimes categorized as either discretionary or non-discretionary. The three most widely recognized models are Discretionary Access Control (DAC), Mandatory Access Control (MAC), and Role Based Access Control (RBAC). MAC and RBAC are both non-discretionary.
Attribute-based access control
In attribute-based access control (ABAC), access is granted not based on the rights of the subject associated with a user after authentication, but based on attributes of the user. The user has to prove so called claims about his attributes to the access control engine. An attribute-based access control policy specifies which claims need to be satisfied in order to grant access to an object. For instance the claim could be "older than 18" . Any user that can prove this claim is granted access. Users can be anonymous as authentication and identification are not strictly required. One does however require means for proving claims anonymously. This can for instance be achieved using anonymous credentials or XACMLXACML
XACML stands for eXtensible Access Control Markup Language. The standard defines a declarative access control policy language implemented in XML and a processing model describing how to evaluate authorization requests according to the rules defined in policies.As a published standard...
(extensible access control markup language).
Discretionary access control
Discretionary access controlDiscretionary access control
In computer security, discretionary access control is a kind of access control defined by the Trusted Computer System Evaluation Criteria "as a means of restricting access to objects based on the identity of subjects and/or groups to which they belong...
(DAC) is an access policy determined by the owner of an object. The owner decides who is allowed to access the object and what privileges they have.
Two important concepts in DAC are
- File and data ownership: Every object in the system has an owner. In most DAC systems, each object's initial owner is the subject that caused it to be created. The access policy for an object is determined by its owner.
- Access rights and permissions: These are the controls that an owner can assign to other subjects for specific resources.
Access controls may be discretionary in ACL-based
Access control list
An access control list , with respect to a computer file system, is a list of permissions attached to an object. An ACL specifies which users or system processes are granted access to objects, as well as what operations are allowed on given objects. Each entry in a typical ACL specifies a subject...
or capability-based
Capability-based security
Capability-based security is a concept in the design of secure computing systems, one of the existing security models. A capability is a communicable, unforgeable token of authority. It refers to a value that references an object along with an associated set of access rights...
access control systems. (In capability-based systems, there is usually no explicit concept of 'owner', but the creator of an object has a similar degree of control over its access policy.)
Mandatory access control
Mandatory access controlMandatory access control
In computer security, mandatory access control refers to a type of access control by which the operating system constrains the ability of a subject or initiator to access or generally perform some sort of operation on an object or target...
refers to allowing access to a resource if and only if rules exist that allow a given user to access the resource. It is difficult to manage but its use is usually justified when used to protect highly sensitive information. Examples include certain government and military information. Management is often simplified (over what can be required) if the information can be protected using hierarchical access control, or by implementing sensitivity labels. What makes the method "mandatory" is the use of either rules or sensitivity labels.
- Sensitivity labels: In such a system subjects and objects must have labels assigned to them. A subject's sensitivity label specifies its level of trust. An object's sensitivity label specifies the level of trust required for access. In order to access a given object, the subject must have a sensitivity level equal to or higher than the requested object.
- Data import and export: Controlling the import of information from other systems and export to other systems (including printers) is a critical function of these systems, which must ensure that sensitivity labels are properly maintained and implemented so that sensitive information is appropriately protected at all times.
Two methods are commonly used for applying mandatory access control:
- Rule-based (or label-based) access control: This type of control further defines specific conditions for access to a requested object. A Mandatory Access Control system implements a simple form of rule-based access control to determine whether access should be granted or denied by matching:
- An object's sensitivity label
- A subject's sensitivity label
- Lattice-based access controlLattice-Based Access ControlIn computer security, lattice-based access control is a complex access control model based on the interaction between any combination of objects and subjects .In this type of label-based mandatory access control model, a lattice is used to define the levels of security...
: These can be used for complex access control decisions involving multiple objects and/or subjects. A lattice model is a mathematical structure that defines greatest lower-bound and least upper-bound values for a pair of elements, such as a subject and an object.
Few systems implement MAC; XTS-400
XTS-400
The XTS-400 is a multi-level secure computer operating system. It is multi-user and multitasking. It works in networked environments and supports Gigabit Ethernet and both IPv4 and IPv6....
and SELinux are examples of systems that do. The computer system at the company in the film Tron
Tron
-Film:*Tron , a franchise that began in 1982 with the Walt Disney Pictures film Tron** Tron , a 1982 science fiction film by Disney, starring Jeff Bridges, Bruce Boxleitner, Cindy Morgan, Dan Shor and David Warner...
is an example from the prior century.
Role-based access control
Role-based access controlRole-Based Access Control
In computer systems security, role-based access control is an approach to restricting system access to authorized users. It is used by the majority of enterprises with more than 500 employees, and can be implemented via mandatory access control or discretionary access control...
(RBAC) is an access policy determined by the system, not the owner. RBAC is used in
commercial applications and also in military systems, where multi-level security requirements may also exist.
RBAC differs from DAC in that DAC allows users to control access to their resources, while in RBAC, access is controlled
at the system level, outside of the user's control. Although RBAC is non-discretionary, it can be distinguished from
MAC primarily in the way permissions are handled. MAC controls read and write permissions based on a user's clearance level and additional labels. RBAC controls collections of permissions that may include complex operations
such as an e-commerce transaction, or may be as simple as read or write. A role in RBAC can be viewed as a set of
permissions.
Three primary rules are defined for RBAC:
- Role assignment: A subject can execute a transaction only if the subject has selected or been assigned a role.
- Role authorization: A subject's active role must be authorized for the subject. With rule 1 above, this rule ensures that users can take on only roles for which they are authorized.
- Transaction authorization: A subject can execute a transaction only if the transaction is authorized for the subject's active role. With rules 1 and 2, this rule ensures that users can execute only transactions for which they are authorized.
Additional constraints may be applied as well, and roles can be combined in a hierarchy where higher-level roles subsume permissions owned by sub-roles.
Most IT vendors offer RBAC in one or more products.
Telecommunication
In telecommunicationTelecommunication
Telecommunication is the transmission of information over significant distances to communicate. In earlier times, telecommunications involved the use of visual signals, such as beacons, smoke signals, semaphore telegraphs, signal flags, and optical heliographs, or audio messages via coded...
, the term access control is defined in U.S. Federal Standard 1037C
Federal Standard 1037C
Federal Standard 1037C, titled Telecommunications: Glossary of Telecommunication Terms is a United States Federal Standard, issued by the General Services Administration pursuant to the Federal Property and Administrative Services Act of 1949, as amended....
with the following meanings:
- A service feature or technique used to permit or deny use of the components of a communication systemSystemSystem is a set of interacting or interdependent components forming an integrated whole....
. - A technique used to define or restrict the rights of individuals or application programs to obtain dataDataThe term data refers to qualitative or quantitative attributes of a variable or set of variables. Data are typically the results of measurements and can be the basis of graphs, images, or observations of a set of variables. Data are often viewed as the lowest level of abstraction from which...
from, or place data onto, a storage deviceData storage devicethumb|200px|right|A reel-to-reel tape recorder .The magnetic tape is a data storage medium. The recorder is data storage equipment using a portable medium to store the data....
. - The definition or restriction of the rights of individuals or application programs to obtain data from, or place data into, a storage deviceStorage deviceStorage device may refer to:*Box, or any of a variety of containers or receptacles*Data storage device, a device for recording information, which could range from handwriting to video or acoustic recording, or to electromagnetic energy modulating magnetic tape and optical discs* Object storage...
. - The process of limiting access to the resources of an AISAutomated information systemThe term automated information system means an assembly of computer hardware, software, firmware, or any combination of these, configured to accomplish specific information-handling operations, such as communication, computation, dissemination, processing, and storage of information...
to authorized users, programs, processes, or other systems. - That function performed by the resource controller that allocates system resources to satisfy userUser (telecommunications)In telecommunications, a user is a person, organization, or other entity that employs the services provided by a telecommunication system, or by an information processing system, for transfer of information....
requests.
This definition depends on several other technical terms from Federal Standard 1037C.
Public policy
In public policyPolicy
A policy is typically described as a principle or rule to guide decisions and achieve rational outcome. The term is not normally used to denote what is actually done, this is normally referred to as either procedure or protocol...
, access control to restrict access to systems ("authorization
Authorization
Authorization is the function of specifying access rights to resources, which is related to information security and computer security in general and to access control in particular. More formally, "to authorize" is to define access policy...
") or to track or monitor behavior within systems ("accountability
Accountability
Accountability is a concept in ethics and governance with several meanings. It is often used synonymously with such concepts as responsibility, answerability, blameworthiness, liability, and other terms associated with the expectation of account-giving...
") is an implementation feature of using trusted systems for security
Security
Security is the degree of protection against danger, damage, loss, and crime. Security as a form of protection are structures and processes that provide or improve security as a condition. The Institute for Security and Open Methodologies in the OSSTMM 3 defines security as "a form of protection...
or social control
Social control
Social control refers generally to societal and political mechanisms or processes that regulate individual and group behavior, leading to conformity and compliance to the rules of a given society, state, or social group. Many mechanisms of social control are cross-cultural, if only in the control...
.
See also
- Access badgeAccess badgeAn access badge is a credential used to gain entry to an area having automated access control entry points. Entry points may be doors, turnstiles, parking gates or other barriers....
- Access control vestibuleAccess control vestibuleThe Access Control Vestibule is a security screening system for the detection of individuals carrying weapons into any facility without authorization, therefore minimizing the possibility of an armed takeover. The ACV is composed of an aluminum frame, separate entrance and exit doors, a metal...
- Alarm devices
- Alarm managementAlarm managementAlarm management is the application of human factors along with instrumentation engineering and systems thinking to manage the design of an alarm system to increase its usability...
- Bank vaultBank vaultA bank vault is a secure space where money, valuables, records, and documents can be stored. It is intended to protect their contents from theft, unauthorized use, fire, natural disasters, and other threats, just like a safe...
- BiometricsBiometricsBiometrics As Jain & Ross point out, "the term biometric authentication is perhaps more appropriate than biometrics since the latter has been historically used in the field of statistics to refer to the analysis of biological data [36]" . consists of methods...
- Burglar alarmBurglar alarmBurglar , alarms are systems designed to detect unauthorized entry into a building or area. They consist of an array of sensors, a control panel and alerting system, and interconnections...
- Card readerCard readerA card reader is a data input device that reads data from a card-shaped storage medium. Historically, paper or cardboard punched cards were used throughout the first several decades of the computer industry to store information and programs for computer system, and were read by punched card readers...
- CastleCastleA castle is a type of fortified structure built in Europe and the Middle East during the Middle Ages by European nobility. Scholars debate the scope of the word castle, but usually consider it to be the private fortified residence of a lord or noble...
- Common Access CardCommon Access CardThe Common Access Card is a United States Department of Defense smart card issued as standard identification for active-duty military personnel, reserve personnel, civilian employees, other non-DoD government employees, state employees of the National Guard, and eligible contractor personnel.The...
- Computer securityComputer securityComputer security is a branch of computer technology known as information security as applied to computers and networks. The objective of computer security includes protection of information and property from theft, corruption, or natural disaster, while allowing the information and property to...
- CredentialCredentialA credential is an attestation of qualification, competence, or authority issued to an individual by a third party with a relevant or de facto authority or assumed competence to do so....
- Door securityDoor securityDoor security relates to prevention of door-related burglaries. Such break-ins take place in various forms, and in a number of locations; ranging from front, back and side doors to garage doors.- Common residential door types :...
- Electronic lockElectronic lockAn electronic lock is a locking device which operates by means of electric current. Electric locks are sometimes stand-alone with an electronic control assembly mounted directly to the lock. More often electric locks are connected to an access control system...
- FortificationFortificationFortifications are military constructions and buildings designed for defence in warfare and military bases. Humans have constructed defensive works for many thousands of years, in a variety of increasingly complex designs...
- Htaccess
- ID Card
- IP ControllerIP access controllerIP access controller is an electronic security device designed to identify users and control entry to or exit from protected areas. A typical IP access controller supports 2 or 4 basic access control readers...
- IP readerIP readerIP reader is an electronic security device designed to identify users and control entry to or exit from protected areas.-Operation:An IP reader has two features that distinguish it from other access control readers:...
- Key cards
- key managementKey managementKey management is the provisions made in a cryptography system design that are related to generation, exchange, storage, safeguarding, use, vetting, and replacement of keys. It includes cryptographic protocol design, key servers, user procedures, and other relevant protocols.Key management concerns...
- Lock smithing
- Lock pickingLock pickingLock picking is the art of unlocking a lock by analyzing and manipulating the components of the lock device, without the original key. Although lock picking can be associated with criminal intent, it is an essential skill for a locksmith...
- Logical securityLogical securityLogical Security consists of software safeguards for an organization’s systems, including user identification and password access, authentication, access rights and authority levels. These measures are to ensure that only authorized users are able to perform actions or access information in a...
- Magnetic stripe cardMagnetic stripe cardA magnetic stripe card is a type of card capable of storing data by modifying the magnetism of tiny iron-based magnetic particles on a band of magnetic material on the card...
- Optical turnstileOptical turnstileAn optical turnstile is a physical security device designed to restrict or control access to a building or secure area. Optical turnstiles are usually a part of an access control system, which also consists of software, card readers, and controllers...
- Photo identificationPhoto identificationPhoto identification is generally used to define any form of identity document that includes a photograph of the holder.Some countries use a government issued card as a proof of age or citizenship.Types of photo ID cards include:*Passports...
- Physical key management
- Physical Security ProfessionalPhysical Security ProfessionalA Physical Security Professional is a certification process for individuals involved in the physical security of organizations. This certification process is offered by ASIS International...
- PrisonPrisonA prison is a place in which people are physically confined and, usually, deprived of a range of personal freedoms. Imprisonment or incarceration is a legal penalty that may be imposed by the state for the commission of a crime...
- Proximity cardProximity cardProximity card is a generic name for contactless integrated circuit devices used for security access or payment systems. The standard can refer to the older 125 kHz devices or the newer 13.56 MHz contactless RFID cards, most commonly known as contactless smartcards.Modern proximity cards...
- Razor wireRazor wireBarbed tape or razor wire is a mesh of metal strips with sharp edges whose purpose is to prevent passage by humans. The term "razor wire", through long usage, has generally been used to describe barbed tape products...
- SafeSafeA safe is a secure lockable box used for securing valuable objects against theft or damage. A safe is usually a hollow cuboid or cylinder, with one face removable or hinged to form a door. The body and door may be cast from metal or formed out of plastic through blow molding...
- Safe-crackingSafe-crackingSafe-cracking is the process of opening a safe without either the combination or key. It may also refer to a computer hacker's attempts to break into a secured computer system, in which case it may be shortened to "cracking" or black hat hacking....
- SecuritySecuritySecurity is the degree of protection against danger, damage, loss, and crime. Security as a form of protection are structures and processes that provide or improve security as a condition. The Institute for Security and Open Methodologies in the OSSTMM 3 defines security as "a form of protection...
- Security engineeringSecurity engineeringSecurity engineering is a specialized field of engineering that focuses on the security aspects in the design of systems that need to be able to deal robustly with possible sources of disruption, ranging from natural disasters to malicious acts...
- Security lightingSecurity lightingIn the field of physical security, security lighting is often used as a preventative and corrective measure against intrusions or other criminal activity on a physical piece of property. Security lighting may be provided to aid in the detection of intruders, to deter intruders, or in some cases...
- Security ManagementSecurity ManagementSecurity Management magazine is the monthly publication of ASIS International . The publication combines feature articles on topics such as terrorism and corporate espionage with staff-written departments covering news and trends, homeland security, IT security, and legal developments.-External...
- Security policySecurity policySecurity policy is a definition of what it means to be secure for a system, organization or other entity. For an organization, it addresses the constraints on behavior of its members as well as constraints imposed on adversaries by mechanisms such as doors, locks, keys and walls...
- Smart cardSmart cardA smart card, chip card, or integrated circuit card , is any pocket-sized card with embedded integrated circuits. A smart card or microprocessor cards contain volatile memory and microprocessor components. The card is made of plastic, generally polyvinyl chloride, but sometimes acrylonitrile...
- Swipe card
- Wiegand effectWiegand effectThe Wiegand effect is a nonlinear magnetic effect, named after its discoverer John R. Wiegand, produced in specially annealed and hardened wire called Wiegand wire....
- XACMLXACMLXACML stands for eXtensible Access Control Markup Language. The standard defines a declarative access control policy language implemented in XML and a processing model describing how to evaluate authorization requests according to the rules defined in policies.As a published standard...
External links
- eXtensible Access Control Markup Language. An OASIS standard language/model for access control. Also XACMLXACMLXACML stands for eXtensible Access Control Markup Language. The standard defines a declarative access control policy language implemented in XML and a processing model describing how to evaluate authorization requests according to the rules defined in policies.As a published standard...
.

